AVAILABLE 24x7
888.662.2724
AVAILABLE 24x7
(888) 66CARAH
Fast & Accurate
Request A Quote
Quick Response
Chat With Us
̽����Ƶ, in conjunction with its vendor partners, sponsors hundreds of events each year, ranging from webcasts and tradeshows to executive roundtables and technology forums.
Events and Resources
Events

Voyager Labs
Empowering Anti-Heroin Task Forces with OSINT: Uncovering Hidden Drug Networks
Event Date: December 10, 2024
Hosted By: Voyager Labs & ̽����Ƶ
Hosted By: Voyager Labs & ̽����Ƶ
During this webinar attendees learned about Voyager, an advanced OSINT tool for law enforcement to uncover, analyze, and dismantle drug networks. Voyager uses social media, forums, and the dark web to track drug sales, trafficking patterns, and networks. Discover how its AI-powered analytics can accelerate investigations and enhance your agency's impact.
During this presentation attendees:
- Learned to Identify Drug Sales and Networks: Discover how Voyager can help you detect drug trafficking activity across social media and online communities
- Track Trafficking Patterns in Real Time: Used Voyager’s mapping and timeline tools to visualize and follow the movements of drug networks as they happen
- Uncovered Hidden Connections in Criminal Organizations: See how Voyager’s advanced analytics reveal the links between individuals and groups, even when they attempt to hide their public footprint
- Enhance Interagency Collaboration: Gained insights into Voyager’s data-sharing capabilities, enabling seamless collaboration with federal, state, and local partners
- Preserve Critical Evidence: Learned to understand Voyager’s data capture features that ensure information remains available, even if scrubbed from public sources
Fill out the form below to view this archived event.
Resources
Featured
The discourse around secure mobile communication platforms has escalated in the United States public sector, where security and data integrity aren’t just priorities but mandates. As agencies become increasingly dependent on digital technologies to execute their missions, the need for secure p...

SBOM360 Hub is the tech industry's first SBOM exchange for complex software. The Hub allows publishes to manage, create, publish, and share software that is compliant with SBOMs standards data along the distribution chain. This enables risk reduction and safe transfer of data.

SBOM360 shows you "what's in your software" by recognizing its software supply chain while looking for risks. Lineaje AI produces solutions and plans if the vulnerabilities of the software are exposed. Reducing risks and cost by 40%.
Government agencies are facing increasing demands to provide services more efficiently, transparently, and with limited resources. To support this transformation, we're thrilled to share that Accela has acquired ePermitHub—marking a significant advancement in streamlining permitting and pl...

The Wiz + Accenture Responsive Protection System — a modern, unified cloud security platform tailored for federal agencies. A simple and secure way to enhance cloud security while reducing costs.
This resource provides an overview of EdgeRunner AI, a military-specific AI solution offering capabilities such as offline, multi-step, multi-turn interactions tailored for warfighters. It highlights features like EdgeRunner Athena for document summarization and domain-specific adapters with LoRA fi...
Access this Cohesity eBook to uncover six key predictions shaping the future of AI, data security, and cloud. As AI rapidly transforms industries, it brings both opportunities and risks—Cohesity experts provide actionable insights to help you stay ahead. Explore practical takeaways and valuabl...
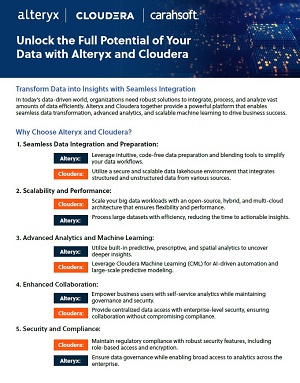
This Alteryx and Cloudera resource highlights their joint solution for seamless data integration, advanced analytics, and scalable machine learning. It emphasizes key benefits such as efficient data processing, secure collaboration, and regulatory compliance, helping businesses optimize decision-mak...
This article discusses the nature of how cybercriminals attack, from the inside! Cybercriminals use legitimate platforms to infiltrate your data. CyberFOX goes into detail on how you can stop these attacks from surfacing,

This article discusses how cyber- privileges affect access to educational institutions data. Phishing, Malware and Lack of Awareness can play a major factor in poor self-defense against cyber-attacks.